|
multifactor authentication (MFA) |
|
Multifactor
authentication (MFA) is a security technology that requires multiple methods
of authentication from independent categories of credentials to verify a
user's identity for a login or other transaction. Multifactor authentication
combines two or more independent credentials: what the user knows, such as a
password; what the user has,
such as a security token; and what the user is, by using biometric verification
methods. The
goal of MFA is to create a layered defense that makes it more difficult for
an unauthorized person to access a target, such as a physical location,
computing device, network or database. If one factor is compromised or
broken, the attacker still has at least one or more barriers to breach before
successfully breaking into the target. In
the past, MFA systems typically relied on two-factor authentication (2FA).
Increasingly, vendors are using the label multifactor
to describe any authentication scheme that requires two or more identity
credentials to decrease the possibility of a cyber attack. Multifactor
authentication is a core component of an identity and access management
framework. Why is multifactor authentication important?One of the biggest shortcomings of traditional user ID and password logins is that passwords can be easily compromised, potentially costing organizations millions of dollars. Brute-force attacks are also a real threat, as bad actors can use automated password cracking tools to guess various combinations of usernames and passwords until they find the right sequence. Although locking an account after a certain number of incorrect login attempts can help protect an organization, hackers have numerous other methods for system access. This is why multifactor authentication is so important, as it can help reduce security risks. MFA authentication methodsAn authentication factor is a category of credential used for identity verification. For MFA, each additional factor is intended to increase the assurance that an entity involved in some kind of communication or requesting access to a system is who -- or what -- it says it is. The use of multiple forms of authentication can help make a hacker's job more difficult. The three most common categories, or authentication factors, are often described as something you know, or the knowledge factor; something you have, or the possession factor; and something you are, or the inherence factor. MFA works by combining two or more factors from these categories. Knowledge factor. Knowledge-based authentication typically requires the user to answer a personal security question. Knowledge factor technologies generally include passwords, four-digit personal identification numbers (PINs) and one-time passwords (OTPs). Typical user scenarios include the following:
Possession factor. Users must have something specific in their possession in order to log in, such as a badge, token, key fob or phone subscriber identity module (SIM) card. For mobile authentication, a smartphone often provides the possession factor in conjunction with an OTP app. Possession factor technologies include the following:
Typical possession factor user scenarios include the following:
Inherence factor. Any biological traits the user has that are confirmed for login. Inherence factor technologies include the following Biometric verification methods:
Biometric device components include a reader, a database and software to convert the scanned biometric data into a standardized digital format and to compare match points of the observed data with stored data. Typical inherence factor scenarios include the following:
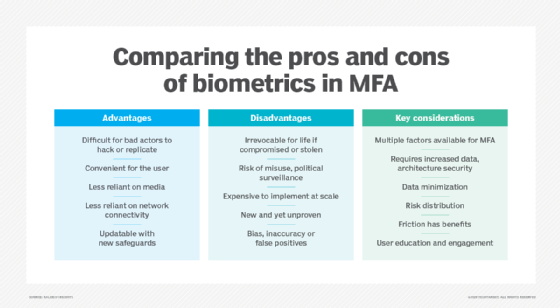
User location is often suggested as a fourth factor for authentication. Again, the ubiquity of smartphones can help ease the authentication burden: Users typically carry their phones, and all basic smartphones have Global Positioning System tracking, providing credible confirmation of the login location. Time-based authentication is also used to prove a person's identity by detecting presence at a specific time of day and granting access to a certain system or location. For example, bank customers cannot physically use their ATM card in the U.S. and then in Russia 15 minutes later. These types of logical locks can be used to help prevent many cases of online bank fraud. What are the pros and cons of MFA?Multifactor authentication was introduced to harden security access to systems and applications through hardware and software. The goal was to authenticate the identity of users and to assure the integrity of their digital transactions. The downside to MFA is that users often forget the answers to the personal questions that verify their identity, and some users share personal ID tokens and passwords. MFA has other benefits and disadvantages. Pros
Cons
Multifactor authentication vs. two-factor authenticationWhen authentication strategies were first introduced, the intent was to enforce security but to also keep it as simple as possible. Users were asked to supply only two forms of security keys that would inform a system that they were authentic and authorized users. Common forms of 2FA were user ID and password or automated teller machine (ATM) bank card and PIN. Unfortunately, hackers quickly discovered ways to buy or break passwords or to skim debit cards at ATMs. This prompted companies and security vendors to look for more hardened forms of user authentication that used additional security factors for verification. Addressing the challenges of multifactor authenticationAdding security factors to MFA further complicates ease of use for users who must remember multiple passwords. Consequently, the goal of MFA is to simplify MFA techniques for users. Here are three approaches being used to simplify MFA:
Learn more about application login weaknesses that are often overlooked during penetration testing. |